A Google-led research paper has reignited fears that quantum computers could one day break Bitcoin’s cryptography, but the actual science tells a far less dramatic story. The bitcoin quantum threat remains theoretical, and the gap between laboratory breakthroughs and real-world attacks on the network is measured in years, not months.
Why the Bitcoin Quantum Threat Is Widely Misunderstood
The phrase “bitcoin quantum threat” refers to the possibility that a sufficiently powerful quantum computer could derive a Bitcoin private key from its corresponding public key, allowing an attacker to spend someone else’s coins. That is a specific, narrow attack vector, not a general “hack all of Bitcoin” scenario.
A Google-led paper posted to arXiv on March 30, 2026 estimated that Shor’s algorithm could run at cryptographically relevant scale with as few as 10,000 reconfigurable atomic qubits. The same paper modeled discrete logarithms on the P-256 elliptic curve taking a few days on a 26,000-physical-qubit system.
Those numbers sound impressive, but they describe theoretical resource estimates under plausible assumptions, not a working machine that exists today. Sensational headlines skip this distinction entirely, jumping from “fewer qubits than expected” to “your Bitcoin is at risk.”
Not every BTC address is equally exposed. An Ark Invest and Unchained report covered by Cointelegraph found that 65.4% of BTC supply is not vulnerable to future quantum threats, while 34.6% remains in address types where the public key is exposed. The difference matters: a quantum attacker would only threaten coins whose public keys are already visible on-chain.
Why Google Can’t Steal Your BTC Today
Owning advanced quantum hardware does not grant access to Bitcoin private keys. Google’s research describes a theoretical path forward, not a deployed capability. No entity, including Google, has demonstrated a fault-tolerant quantum computer anywhere near the scale required to break elliptic-curve cryptography.
The consensus timeline from IBM, Google, and Microsoft places the first public-key break around the mid-2030s. Google itself has set a 2029 target for migrating its own systems to post-quantum cryptography, a signal that the company treats this as a future planning exercise rather than an immediate operational concern.
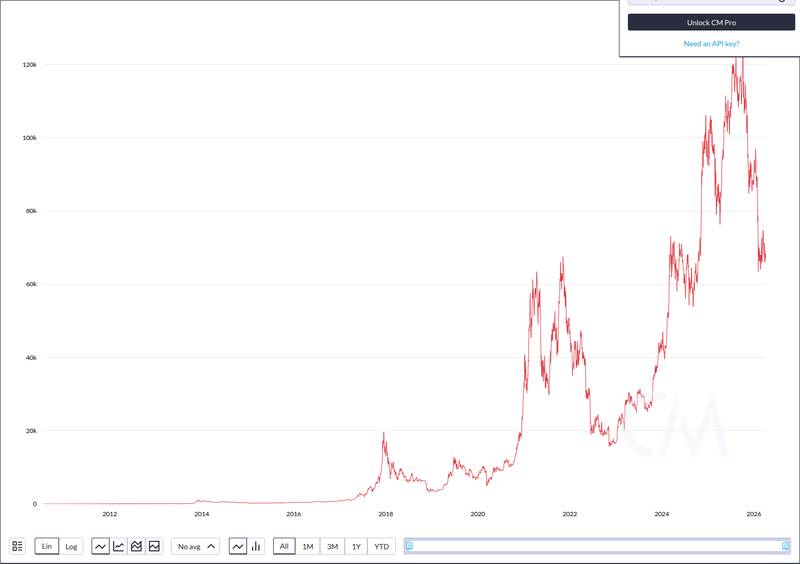
Bitcoin trades at $68,403 with a market cap of roughly $1.37 trillion, and the Fear & Greed Index sits at 11, reflecting extreme fear driven by broader macro concerns, not quantum panic.

The market is not pricing in a quantum emergency. If institutional investors believed Google or any state actor could break Bitcoin’s cryptography imminently, the sell-off would be catastrophic, not a modest 1.8% daily decline.
Bitcoin’s community also has a track record of upgrading the protocol in response to emerging risks. Post-quantum signature schemes like SLH-DSA were standardized by NIST last year, and Bitcoin developers can integrate quantum-resistant options well before any credible mass-theft scenario materializes.
Probably not for 20-40 years, if then. And there are quantum secure signatures, NIST standardized SLH-DSA last year. Bitcoin can add over time, as the evaluation continues and be quantum ready, long before cryptographically relevant quantum computers arrive.
— Adam Back (@adam3us) November 15, 2025
Source: @adam3us on X
Adam Back, a cryptographer whose work predates Bitcoin itself, estimated that cryptographically relevant quantum computers are 20 to 40 years away. That assessment reflects expert judgment rather than settled industry consensus, but it aligns with the broader timeline modeling from major hardware vendors.
What Bitcoin Holders Should Watch Instead of Panicking
Short-term losses in crypto are far more likely to come from scams, exchange failures, or poor key management than from quantum attacks. As crypto apps shut down and billions flow toward Bitcoin ETFs and stablecoins, the real risks center on custodial security and counterparty exposure.
Address reuse is the most relevant quantum-adjacent risk for individual holders. When you reuse a Bitcoin address after spending from it, your public key is permanently exposed on-chain. Using a fresh address for each transaction eliminates this specific attack surface entirely.
Good wallet hygiene, hardware wallets, and avoiding unnecessary exposure of public keys are practical steps that protect against both current threats and any future quantum scenario. These basics matter far more than headline-driven anxiety about which cryptos to buy based on fear cycles.
The longer-term story worth tracking is Bitcoin’s migration path toward quantum-resistant protections. BIP-360, which proposes a framework for post-quantum address types, is one of several proposals under discussion. The protocol has years to prepare, and the development community is already working on it.
Quantum computing will eventually force every cryptographic system to upgrade, from banking infrastructure to Ethereum and newer blockchain protocols. Bitcoin is not uniquely vulnerable; it is one target among thousands, and it has a head start on adaptation.
Disclaimer: This article is for informational purposes only and does not constitute financial or investment advice. Cryptocurrency and digital asset markets carry significant risk. Always do your own research before making decisions.