A reported $285 million exploit of Solana-based Drift Protocol, combined with a fresh scare across the Solana ecosystem, is forcing the crypto industry to confront an uncomfortable possibility: the next major security breach may not come from an anonymous hacker on the outside, but from someone already inside the building.
On April 1, 2026, Drift Protocol publicly disclosed it was experiencing an active attack and immediately suspended deposits and withdrawals. The team said it was coordinating with multiple security firms, bridges, and exchanges to contain the incident. Security firms estimated losses at up to $285 million, though CertiK-tracked visible outflows were lower, and Drift has not yet published a finalized post-mortem with audited loss totals.
Drift Protocol is experiencing an active attack. Deposits and withdrawals have been suspended. We are coordinating with multiple security firms, bridges, and exchanges to contain the incident. This is not an April Fools joke. We’ll provide additional updates from this account as… https://t.co/03SRPq4fHj
— Drift (@DriftProtocol) April 1, 2026
Source: @DriftProtocol on X
Why the Drift hack shifted the security conversation toward insider risk
The scale alone made Drift one of the largest single-protocol exploits in Solana’s history. But the more consequential detail, according to unconfirmed reports, is that the primary root cause may have been an insider compromise rather than a purely external smart-contract exploit.
That distinction matters. Smart-contract bugs are code-level failures that audits can catch. Privileged-access abuse, by contrast, exploits the trust architecture around who can deploy, sign, and move funds. When a deployer key or multisig signer is compromised, no amount of code auditing prevents the damage.
The Drift incident landed during a period of acute market stress. The Fear & Greed Index sat at 17, deep in Extreme Fear territory, amplifying the liquidity shock and withdrawal panic across Solana-native protocols.
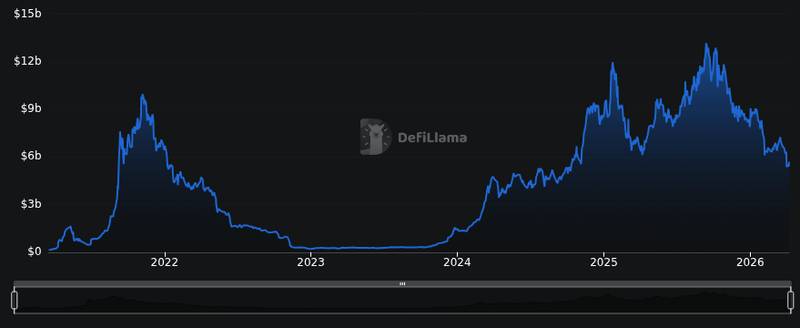
Solana’s total value locked stood at roughly $12.48 billion at the time, meaning a single $285 million exploit represented over 2% of the chain’s entire DeFi collateral base.
What the new Solana scare reveals about insider attack paths
The Drift exploit is not an isolated data point. U.S. law enforcement has documented a pattern of state-backed insider infiltration targeting crypto platforms. The DOJ announced more than $15 million in civil forfeiture actions tied to DPRK-linked virtual-currency laundering, alongside multiple guilty pleas.
Those cases detailed four 2023 virtual-currency platform heists linked to APT38, with individual losses of approximately $37 million, $100 million, $138 million, and $107 million. DOJ Criminal Division’s Matthew R. Galeotti stated that “hostile nation-states raising funds for illicit programs by stealing from digital asset exchanges threatens both” national security and the financial system.
Treasury’s OFAC, along with the FBI and State Department, published an advisory warning firms about North Korean freelance developer infiltration techniques. The advisory outlined how DPRK IT workers use fraudulent identities to gain remote access to protocol codebases and internal tooling, a form of regulatory and operational risk that jurisdictions like Thailand are also tightening scrutiny around.
Three insider attack scenarios stand out for Solana ecosystem projects specifically:
- Compromised deployer or multisig signer: A single compromised key holder can authorize upgrades or withdrawals that bypass governance. Solana’s program upgrade authority model concentrates this risk.
- Internal tooling or dependency pipeline compromise: Build scripts, CI/CD pipelines, and dependency chains are trust surfaces. A malicious contributor with commit access can inject backdoors that survive code review.
- Social engineering against privileged operators: Phishing, fake job offers, and impersonation targeting core team members with signing authority remain the lowest-cost, highest-yield attack vector.
For users, the consequences are immediate: withdrawal pauses, governance disruption, and liquidity shock. The Drift incident demonstrated all three in real time, as deposits and withdrawals were frozen while the team scrambled to assess the damage. Similar dynamics have played out in large-scale institutional crypto movements that trigger sudden liquidity shifts.
SOL traded at $83.47 with a 24-hour trading volume of roughly $5.39 billion, reflecting elevated activity as traders repositioned around the security concerns. The token’s market cap of approximately $47.9 billion underscores the scale of capital exposed to Solana-native protocol risks.

How protocols and users can reduce insider risk right now
KEY TAKEAWAYS
- Insider access, not just code bugs, is emerging as crypto’s most underpriced security risk.
- State-backed actors are actively infiltrating protocol teams through fraudulent developer identities.
- Users should evaluate any protocol’s key management, signer structure, and incident disclosure practices before depositing funds.
Least-privilege access and separation of duties: No single team member should hold both deploy authority and treasury signing power. Multisig thresholds should require a supermajority, and signer identities should be verified through in-person or notarized processes, not just GitHub handles.
Hardware-backed key management and signer rotation: All privileged keys should live on hardware security modules or hardware wallets, never in browser extensions or hot wallets. Regular key rotation limits the window of exposure if a credential is silently compromised.
Continuous monitoring, kill switches, and disclosure standards: Protocols need on-chain monitoring that flags anomalous withdrawal patterns in real time, paired with pre-authorized circuit breakers that can pause contracts before losses compound. The growing focus on community-driven governance in crypto projects also highlights why transparent post-incident disclosure is essential for maintaining user trust.
No public post-mortem with finalized loss totals has been released by Drift, and no law enforcement attribution specific to this incident has been confirmed. Until those details emerge, the reported $285 million figure and the insider-compromise theory remain unverified. What is confirmed: the DOJ’s DPRK forfeiture actions, OFAC’s infiltration advisory, and Drift’s own admission that an active attack forced a full operational pause. Together, those facts outline a threat model the industry can no longer afford to treat as theoretical.
Disclaimer: This article is for informational purposes only and does not constitute financial or investment advice. Cryptocurrency and digital asset markets carry significant risk. Always do your own research before making decisions.